
Thanks to Steve Gibson and the Security Now! podcast (SN#551) for the inspiration to turn this console-based utility into a GUI...and to give it a little polish.
Key Benefits
- Hourly scans for all Windows system certificate stores. Reports when changes are made.
Blaser CertWatch
Automated system certificate store checking for
Windows workstation and server. Alerts users
to the addition and removal of system certificates.
CertWatch performs hourly scans of all system certificate stores and will report any additions or deletions from those stores when changes are made.
 |
|
 |
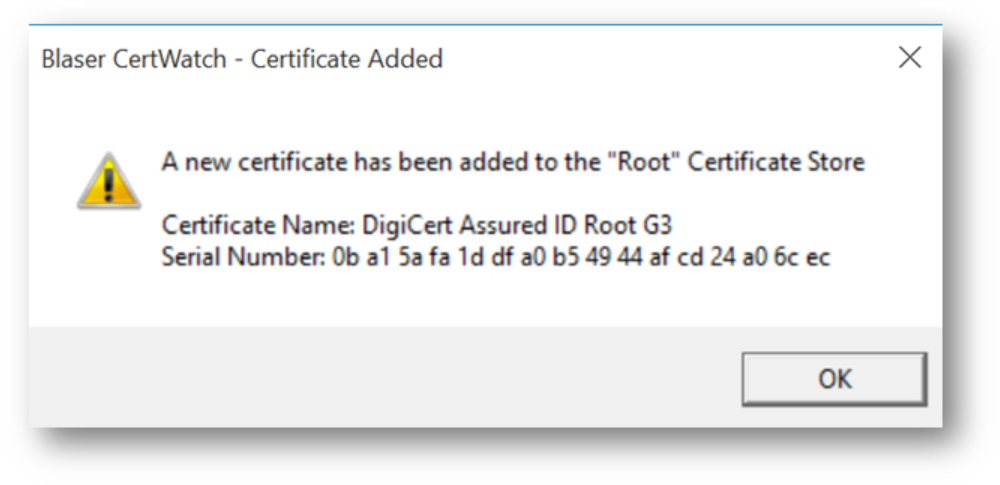
| New certificate added
notification |
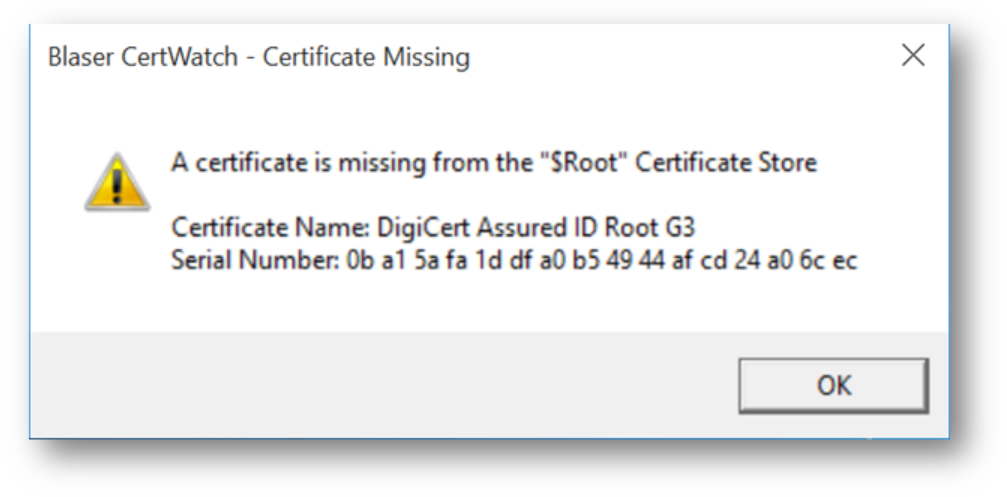
Certificate
missing/deleted notification |
Getting Started
Simply download the single-file executable, and
launch. Easy!
|
|
|
After download,
simply double-click to launch the single-file
executable. |
|
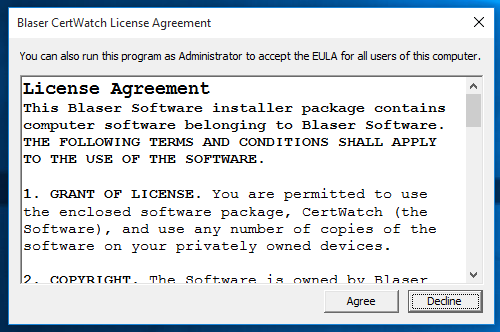 |
Accept the license agreement to
continue. |
||
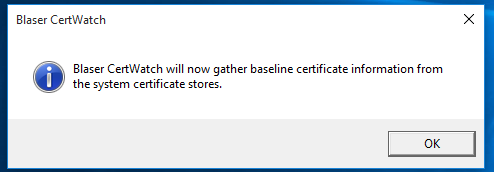 |
Blaser CertWatch will next gather
a baseline by enumerating through all of your
system certificate stores including: • Current User (CERT_SYSTEM_STORE_CURRENT_USER) • Current Service (CERT_SYSTEM_STORE_CURRENT_SERVICE) • Local Machine (CERT_SYSTEM_STORE_LOCAL_MACHINE) • Local Machine Group Policy (CERT_SYSTEM_STORE_LOCAL_MACHINE_GROUP_POLICY) • Current User Group Policy (CERT_SYSTEM_STORE_CURRENT_USER_GROUP_POLICY) • Services (CERT_SYSTEM_STORE_SERVICES) • Users (CERT_SYSTEM_STORE_USERS) • Local Machine Enterprise (CERT_SYSTEM_STORE_LOCAL_MACHINE_ENTERPRISE) |
||
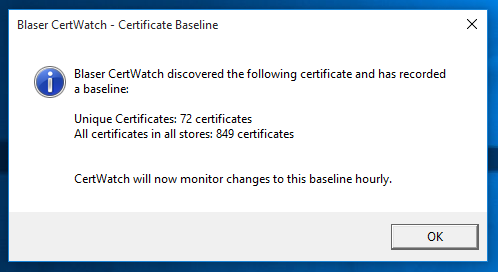 |
Baseline discoveries are reported
to you. |
||
 |
Blaser CertWatch resides in the
system tray. Where it waits vigilantly to
notice and report on certificate activity.
Scans of the system certificate stores are
conducted at program launch and hourly
thereafter. |
||
| Hovering over the tray icon show
the current status. Double-clicking on tray icon opens the detail pane displaying the list of system certificates. |
|||
| Certificate Name,
Serial Number and the count of stores this
certificate is contained within. |
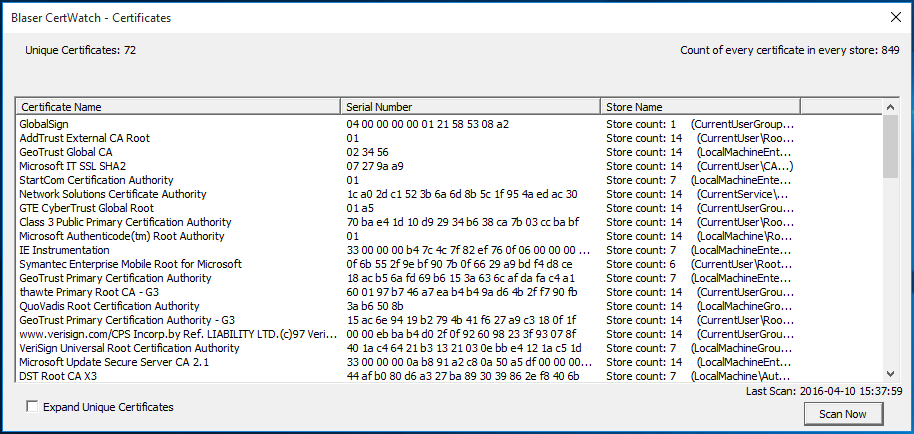 Click the "Scan Now" button to perform an immediate scan of the system certificate stores. |
||
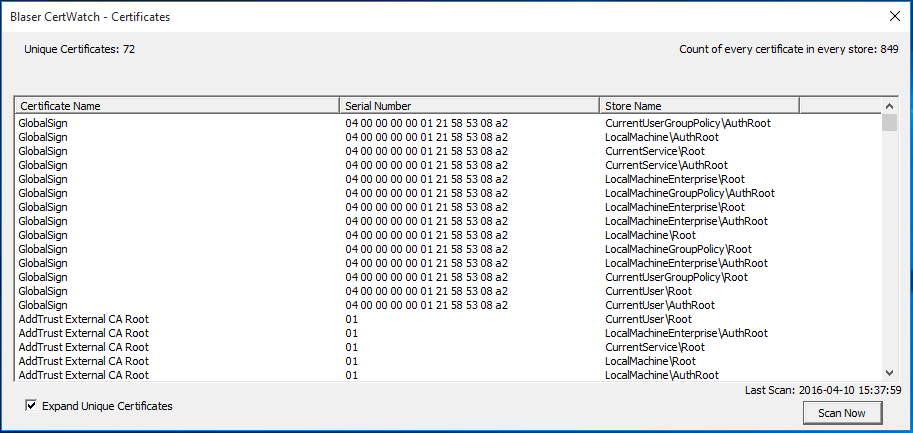
| You can check the "Expand Unique
Certificates" checkbox to display all
occurrences of the certificate across all system
certificate stores. |
|||
 |
|||
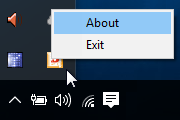 |
Right-click the tray icon to
access the "About" menu. |
||
 |
From the About page, you can
check for updates to Blaser CertWatch. |
||
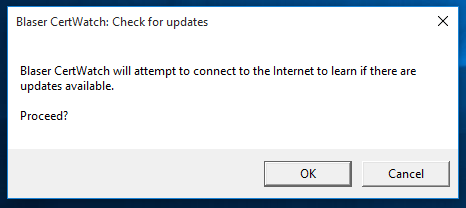 |
Blaser CertWatch will prompt for
your consent before accessing the
Internet. The check for updates function
will retrieve the current version from the
server at www.blaser.us |
|
Download Version 1.0 |
MD5 checksum: 363ae0f54b494869ca45ace94b2d5173
Upcoming plans for the next release include: Automated checking of expired or nearly
expired certificates so that system services
dependent on these certificates will not fail
due to expiration (IIS [HTTPS/TLS], Active
Directory, SChannel services) Ability to run Blaser CertWatch as a
background system service |
|
| |
||
Try some of our other software products...
 |
 |
 |
|
| Blaser
WinUnlock - Unlock Windows workstations
and access user sessions for tech support and
audit controls. |
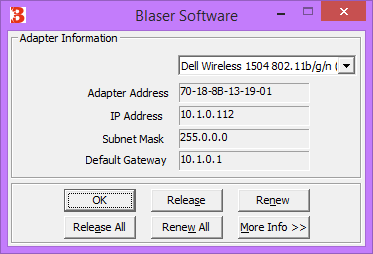
Blaser
Winipcfg - Just like the Win9x
utility. GUI ipconfig for Windows
workstation and server. |
Blaser
RDP Sentinel - monitor and bloc brute
force RDP connections to your Windows servers. |

